Keylogger
-
Upload
elisabethynicole -
Category
Documents
-
view
173 -
download
0
Transcript of Keylogger

LA SEGURIDAD EN INTERNET

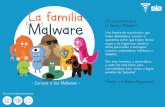
virus


gusanos

troyanos

spyware

adw
are

hijackers

hoaxes

Para proteger la maquina :
Antivirus :
Firewire :

Seguridad en las personas :

Amenazas :
Phising :
Ciberacoso :

Formas de protegernos..
Consejos :

Consejo 1 :Lee las políticas de uso y privacidad de los diferentes servicios antes de utilizarlos.

Consejo 2 :Piensa antes de publicar, no sea que luego te arrepientas.

Consejo 3 :
Valora que información deseas revelar y controla quien puede acceder a ella.

Consejo 4 :Controla tu lista de contactos, y antes de agregar a alguien tomate tu tiempo para asegurarte de su confianza.

Consejo 5 :Las redes sociales contienen las mismas aplicaciones que utilizan los atacantes para propagar los virus –correo, mensajería, navegación, etc.-, mantén las mismas recomendaciones.